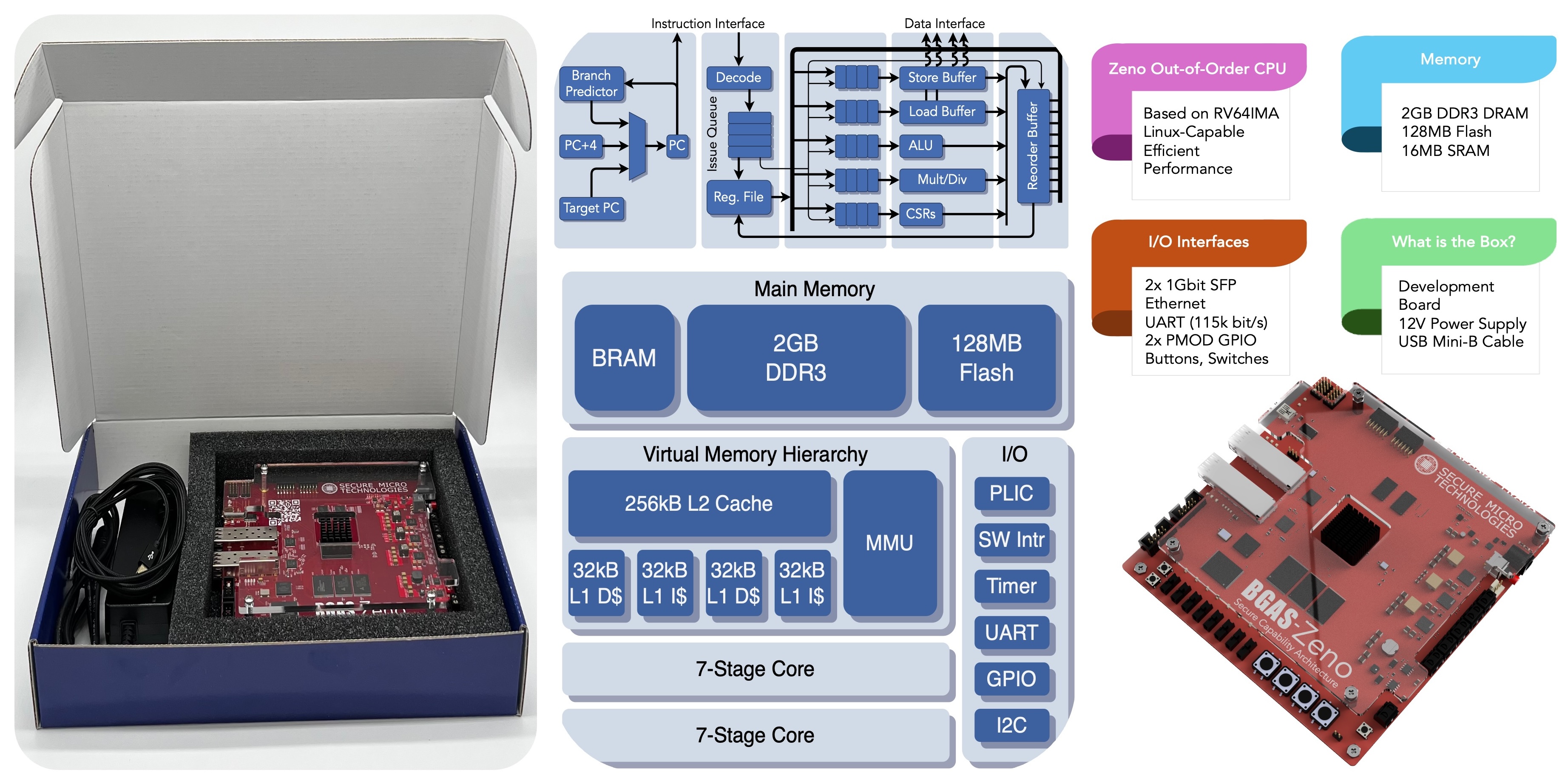
Secure Micro Technologies, LLC is proud to announce the launch of its Itus Bridge™ Module, a groundbreaking hardware solution engineered to support the seamless transition from classical encryption to Post-Quantum Cryptography (PQC). Developed with support from the National Institute of Standards and Technology (NIST), this initiative is designed to enable government and industry networks to adopt the newly standardized PQC Federal Information Processing Standards (FIPS) algorithms with minimal operational disruption.
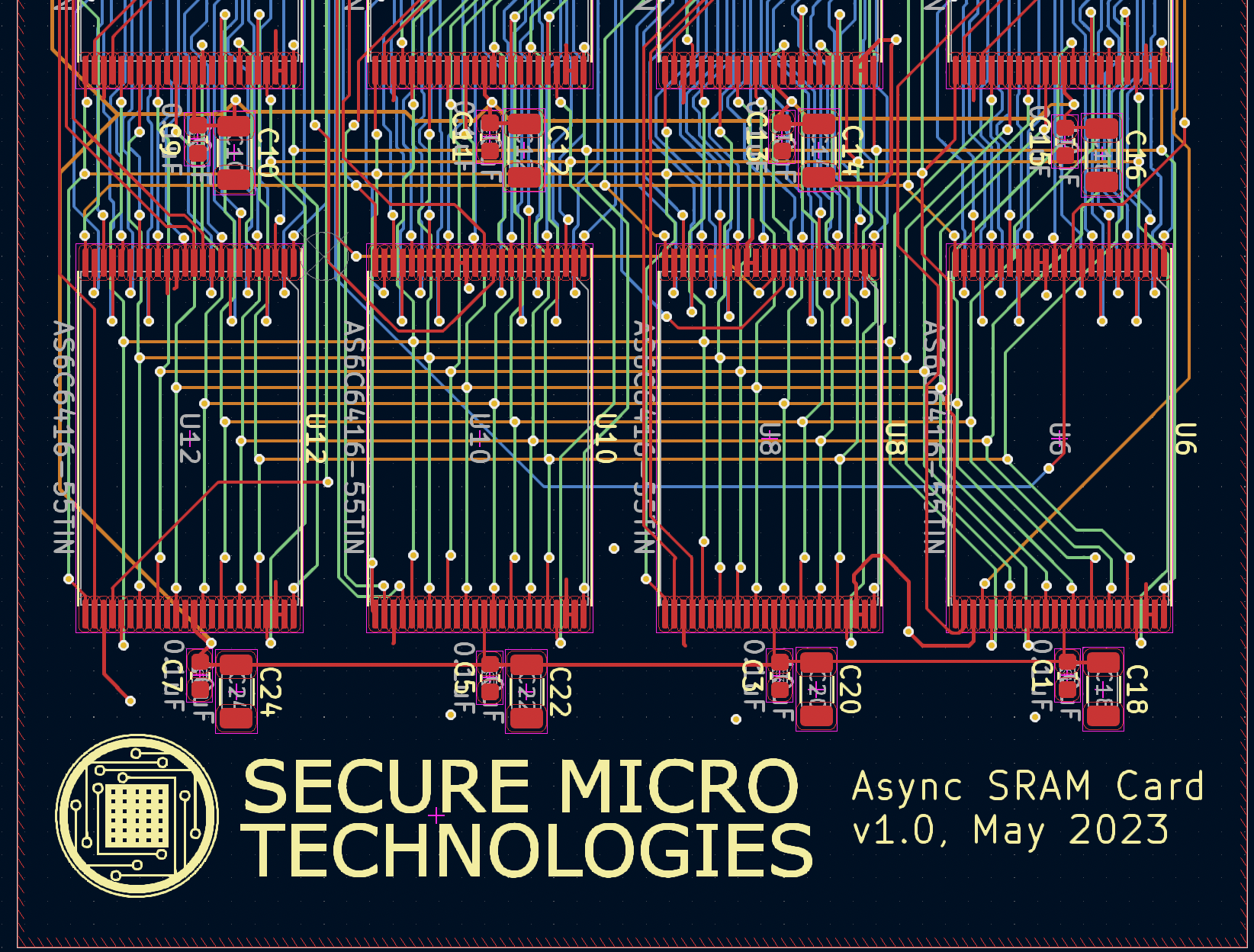
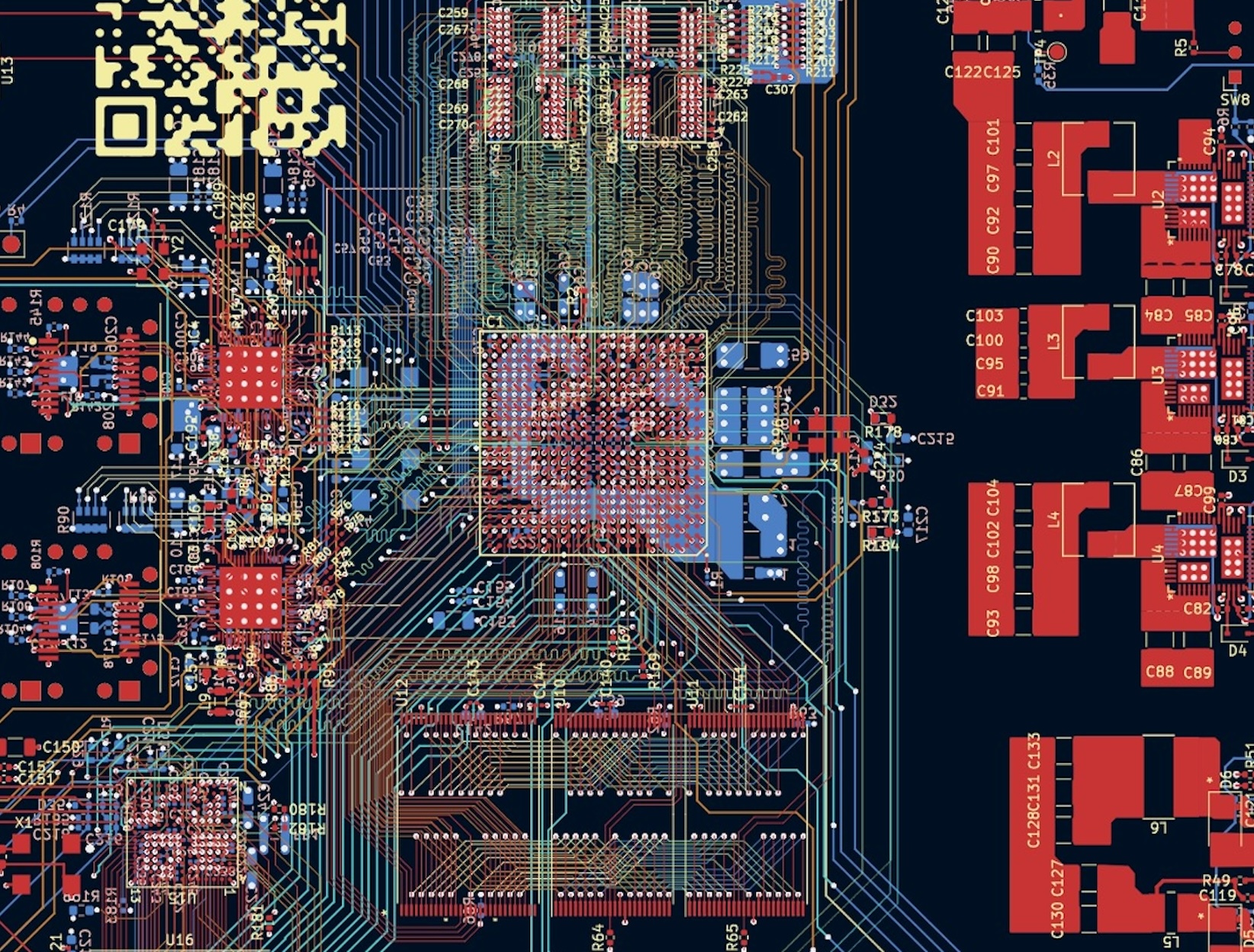
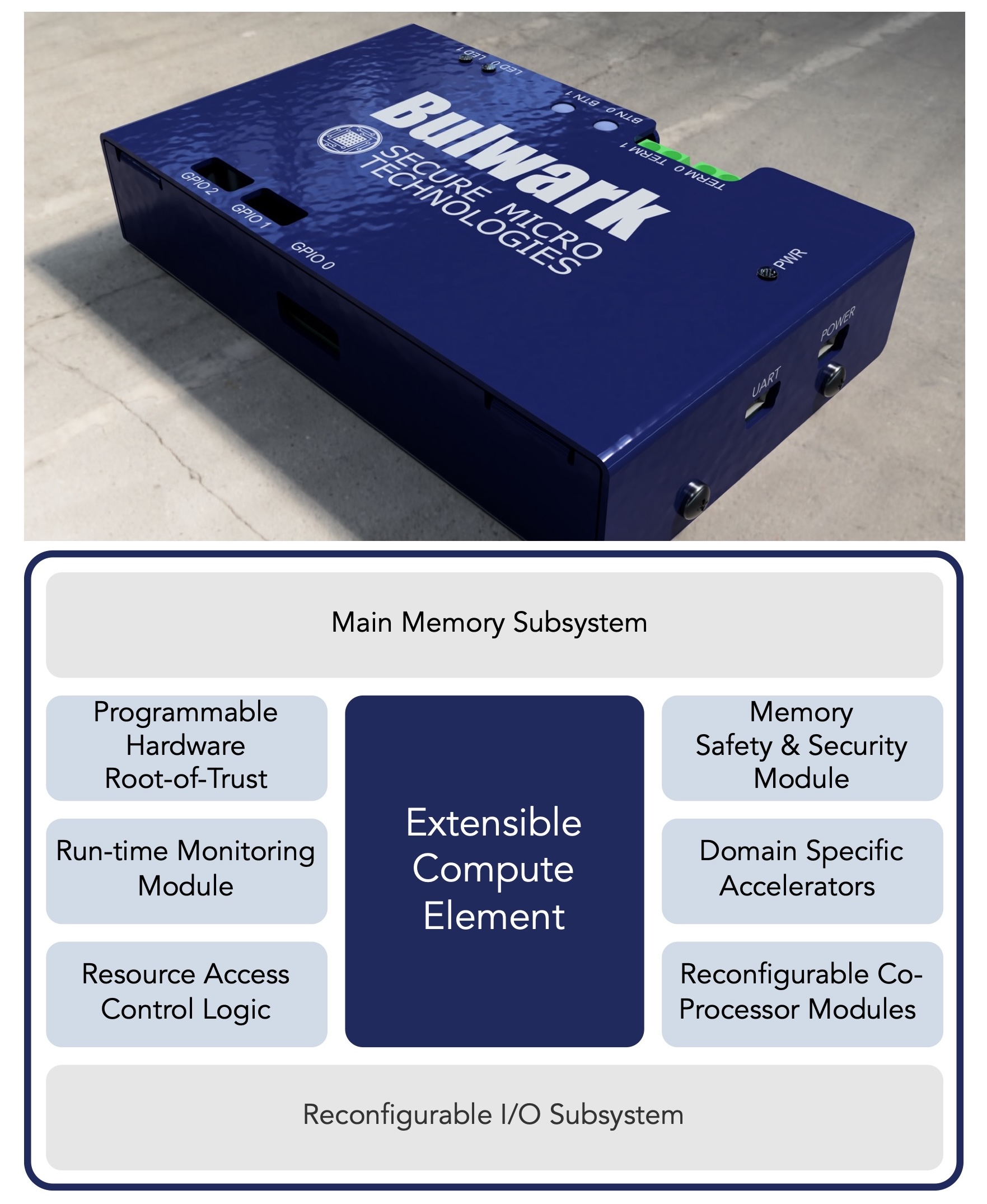
At the heart of the Itus Bridge™ Architecture is a programmable, quantum-resistant Hardware Security Module (PQC-HSM) that integrates two distinct cryptographic domains, one for classical encryption and one for post-quantum encryption, linked through a secure processor core enclave. This architecture enables secure execution, cryptographic acceleration, and flexible programmability, offering a plug-and-play solution for bridging legacy and quantum-secure systems.
“The Itus Bridge™ is a first-of-its-kind platform offering provable security guarantees for interoperability between legacy and quantum-resistant systems,” said Heather Kinsy, President & CEO of Secure Micro Technologies and Principal Investigator on the project. “Our goal is to support a phased, secure transition to PQC across critical infrastructure.”
To accelerate adoption, Secure Micro Technologies is launching an Early Adopter Program, providing prototype Itus Bridge™ modules to select organizations in the defense, aerospace, and critical infrastructure sectors. Participants will gain early access, dedicated technical support, and direct collaboration opportunities with both NIST and Secure Micro’s engineering team.